Perhaps many would consider it an overkill but any thoughts on optionally allowing for 2FA logins using TOTP or WebAuthn in addition to a password?
EDIT: Save yourself the trouble reading down. We already have this. You can enable it in settings.
Perhaps many would consider it an overkill but any thoughts on optionally allowing for 2FA logins using TOTP or WebAuthn in addition to a password?
EDIT: Save yourself the trouble reading down. We already have this. You can enable it in settings.
Ok I am an idiot
These features are both already available.
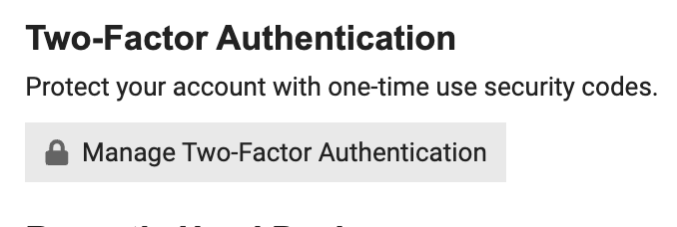
Check the security section of your profile: https://unicyclist.com/my/preferences/security and click Manage Two-Factor Authentication.
TOTP is Token-Based Authenticators and WebAuthn is Security Keys.
Oh, I’m too late! ![]()
My humble pref. No.
That is ok. I am the stupid one. Not sure how I missed this.
well it is optional ![]()
I use it with Authy, it’s pretty cool!
I use Authy too and it is very nice that it has the possibility of securely syncing keys (seeds/secrets) to more than one device (even though this somewhat undermines the 2FA concept [by making a copy of the “thing you have”]).
It is however a bit annoying that their Linux client (which I use because I do not have a smartphone) is snap only. I use a Linux distro without systemd (Slackware) so snap would not be an option for me, even if I did want to use it. However, at a push you can work around this.
mkdir -p ~/.local/share/authy
cd ~/.local/share/authy
wget $(wget -qO- --header Snap-Device-Series:\ 16 https://api.snapcraft.io/v2/snaps/info/authy | grep -io 'https.*/download/[a-z0-9_]*.snap')
☞ Triple-click to select the entire line, above.
unsquashfs -q -f -d . *.snap
rm -r command.sh data-dir desktop-common.sh desktop-gnome-specific.sh desktop-init.sh gnome-platform lib meta/snap.yaml usr *.snap
sed -i "/^Exec=/s,=,=$PWD/,;s,\${SNAP},$PWD," meta/gui/authy.desktop
install -Dm755 meta/gui/authy.desktop ~/.local/share/applications/authy.desktop
☞ You may need to relogin to your desktop environment before authy shows up.
And if you ever want to remove it, just delete ~/.local/share/applications/authy.desktop and the install directory (e.g. ~/.local/share/authy).
The other annoying thing with Authy is that it has no possibility for export of keys. After you get them into the Authy system initially on setup, there is no easy way to get them out, only to sync them to further devices that run Authy. I do not really like that form of lock in. Yes it is possible to get them out but Authy does not provide any officially supported way.
Luckily I note and make a copy of the key (or QR code) when I first setup and then encrypt these with GPG. So if I ever want to setup a new non-Authy device I have that possibility.
In addition to Authy I have a little shell script that calls gpg and fetches the keys and pipes them through mintotp (20 lines of python that can generate OTPs) if I want to list my OTPs on the terminal. This is handy should I want to ssh into my machine remotely and generate them.
As someone who actually writes software changelogs, I must admit stuff like this really annoys me with Authy
Also there is always the concern that after an update you find yourself in a situation like this guy
Which is why lock in is such a problem. What is this guy going to do now if they do not work out the issue? For this reason I would always make a secure copy of the QR code and/or raw key. Thus if you ever need to quickly setup a rival TOTP authentication application you can.
You’re not an idiot after all ![]()
Ok, we have a really advanced linux user here, going through the hassle of avoiding systemd, using slackware and now also 2fa ![]()
I was asking myself the same, whether use 2fa or not. I decided against it as I visit this forum on my smartphone, mostly (de-googled android, btw. Hey, I want to show off, too ![]() ). But I do use keepassxc on linux and keepassdx on android. It offers the service of creating hard to guess but easy to remember passwords via dice ware, very hard to guess and very hard to remember passwords, and also totp (but I did not try it, as using that on the same device as the login screen would indeed undermine 2fa), and I would be really surprised if it did not show up in your linux repos. No syncing of keys, afaik. You can store your passwords and access them with a hard to guess, easy to remember master password, and also insert passwords in your login screens without using the clipboard. I feel this adds a lot of security, whereas using totp on the same device as the website somehow does not, if an attacker got access to your pc. On the other hand, somehow low risk for you, as most attacks aim for windows…
). But I do use keepassxc on linux and keepassdx on android. It offers the service of creating hard to guess but easy to remember passwords via dice ware, very hard to guess and very hard to remember passwords, and also totp (but I did not try it, as using that on the same device as the login screen would indeed undermine 2fa), and I would be really surprised if it did not show up in your linux repos. No syncing of keys, afaik. You can store your passwords and access them with a hard to guess, easy to remember master password, and also insert passwords in your login screens without using the clipboard. I feel this adds a lot of security, whereas using totp on the same device as the website somehow does not, if an attacker got access to your pc. On the other hand, somehow low risk for you, as most attacks aim for windows…
Depends on your threat model. If you are worried about your client device being compromised, then yes, it weakens your position. But there’s an argument to be made that if your client is compromised then it’s already game over.
Even if your password and OTA secret are stored in the same place, 2FA still adds a level of protection against MITM attacks because your login doesn’t depend solely on a long lived secret which is sent over the wire. And MITM attacks are arguably the main thing to worry about on the Internet, since the network is the part that you can’t control.
That is true. But then 2fa again could add some level of security, but only if you store your 2fa secret on another device. If you want security, you should take different forms of attacks into account, especially when you install software manually and probably forget to update it.
If you fear MITM attacks, maybe onion network or vpn could be interesting.
Ok, enough of this for me, I grab my uni now ![]()
I understand that the original question is about allowing 2FA, not about mandating it. In itself, I would not be against allowing it, although I for one would not use it. 1FA is strong enough for me, we’re not talking about the bank here. Note that if simply allowing 2FA would bring simple users like myself into problems like not being able to log in, I would not be in favour of allowing it.
I suspect it has been there since day one of the updated version of the forums, so if it has not bothered you yet, i doubt it will bother you now. ![]()
As for
1FA is strong enough for me, we’re not talking about the bank here.
True and fair enough but the way I see it, if I have already set it up for a few sites it does not add much more hassle for me to use it for others that support it, even if arguably an overkill.
Although, there is some risk. I mean imagine if someone hacked my account and said that bicycles are better than unicycles. Surely this is as bad as someone draining my bank account. Imagine the shame! ![]()
This is actually a benefit of 1FA. I have an escape in case I would write something stupid, like your example or otherwise. I can always blame it on my account having been compromised ![]()
Yikes! That’s a major risk, we’d ban you without any question.
I mean… that sounds fair to be honest ![]()